Cybersecurity Best Practices for Small Businesses Access
Small businesses are prime targets for cyberattacks due to their often-limited resources for robust cybersecurity defenses. However, by implementing some key best practices, small businesses can significantly improve their security posture and protect themselves from costly data breaches and operational disruptions. The first line of defense lies in employee education. Phishing emails and social engineering scams are cunning attempts to trick employees into revealing sensitive information or clicking malicious links. Regular security awareness training empowers employees to recognize these tactics and respond appropriately. This training should cover identifying phishing attempts, password hygiene best practices, and the importance of reporting suspicious activity. Another crucial step is conducting a cybersecurity risk assessment. This helps identify vulnerabilities in your systems, networks, and data storage practices. By understanding your specific risks, you can prioritize your security efforts and allocate resources effectively. Common areas to assess include password strength, software update status, data encryption practices, and physical access controls to devices and servers.

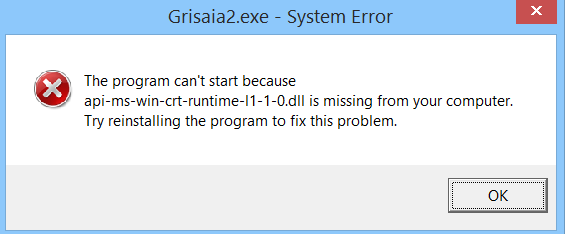
Technical safeguards are equally important. Antivirus and anti-malware software are essential to detect and prevent malware infections. Keeping all software applications, operating systems, and firmware updated with the latest security patches is vital. Cyber Security Hackers exploit known vulnerabilities, so prompt patching is crucial. Firewalls act as a gatekeeper, filtering incoming and outgoing network traffic and blocking unauthorized access attempts. Additionally, consider using a virtual private network VPN to encrypt your internet traffic, especially when using public Wi-Fi. Data security should be a top priority. Implement strong password policies, requiring complex passwords and regular changes. Multi-factor authentication MFA adds an extra layer of security by requiring a second verification factor beyond just a password, like a fingerprint or a code from an authenticator app. Limit employee access to data on a need-to-know basis, granting access only to the information required for their specific roles. Encrypt sensitive data both at rest and in transit to further safeguard it from unauthorized access. Do not neglect physical security measures. Implement access controls to restrict physical entry to critical IT infrastructure.
This can include locked server rooms, secure storage for devices, and employee ID badges for access control systems. Regularly back up your data to a secure offsite location. This ensures you can recover critical information in the event of a cyberattack, hardware failure, or natural disaster. Mobile devices pose a growing security challenge. Develop and enforce a mobile device security policy that requires strong passwords, screen lock timeouts, and regular software updates. Consider deploying mobile device management MDM solutions to centrally manage and secure company-issued devices. Additionally, be cautious about the types of applications employees download and use on business devices. Finally, remember that cybersecurity is an ongoing process. Stay informed about the latest cyber threats and update your security practices accordingly. Regularly test your defenses through penetration testing or vulnerability assessments to identify and address weaknesses before attackers exploit them. By prioritizing cybersecurity and implementing these best practices, small businesses can significantly reduce their risk of cyberattacks and protect their valuable data and operations.